Your first draft is already written.
AI runs ahead of you. Every output that would otherwise need an analyst's first pass is already drafted by the time you open the deal. You review and approve. The work moves at the speed of decisions, not the speed of typing.
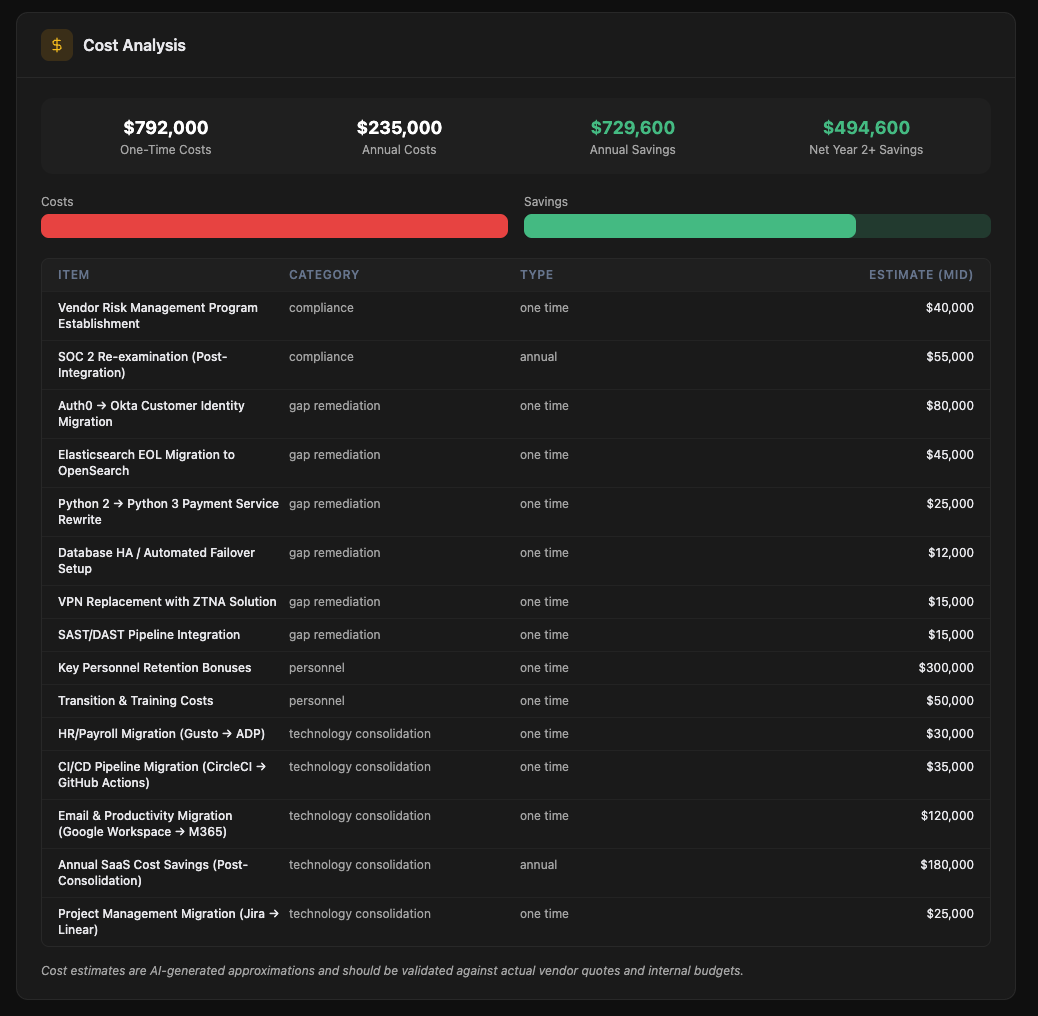
Quantify the integration cost before you sign
Inventory every tool the target runs, identify overlap with your platform stack, and get a clear picture of consolidation savings and integration cost. The numbers that move IRR.
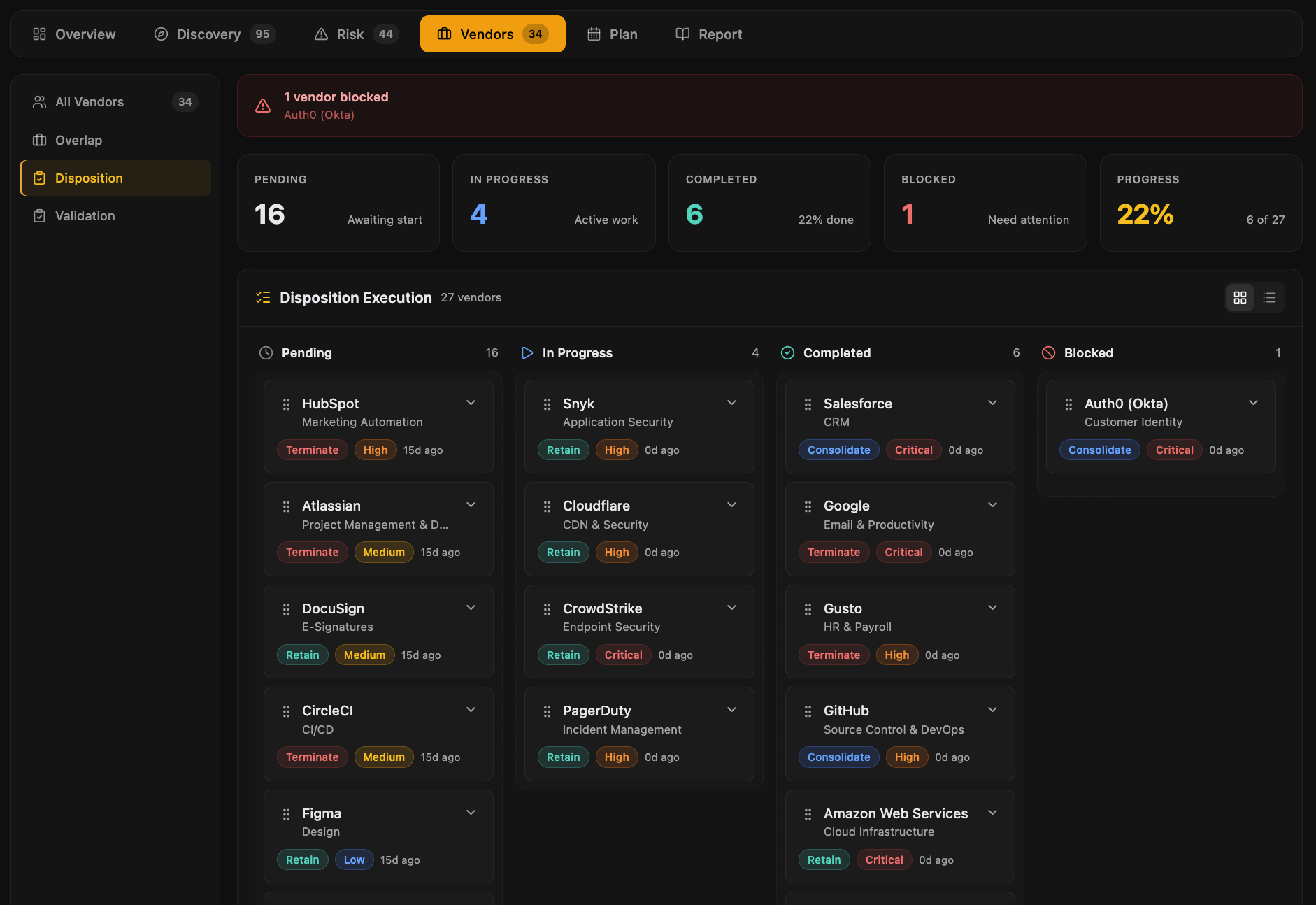
The target's vendors become yours at close
Map every inherited third-party relationship, assess criticality and spend, and make disposition decisions: retain, consolidate, or review, before integration begins. No surprises Day 1.
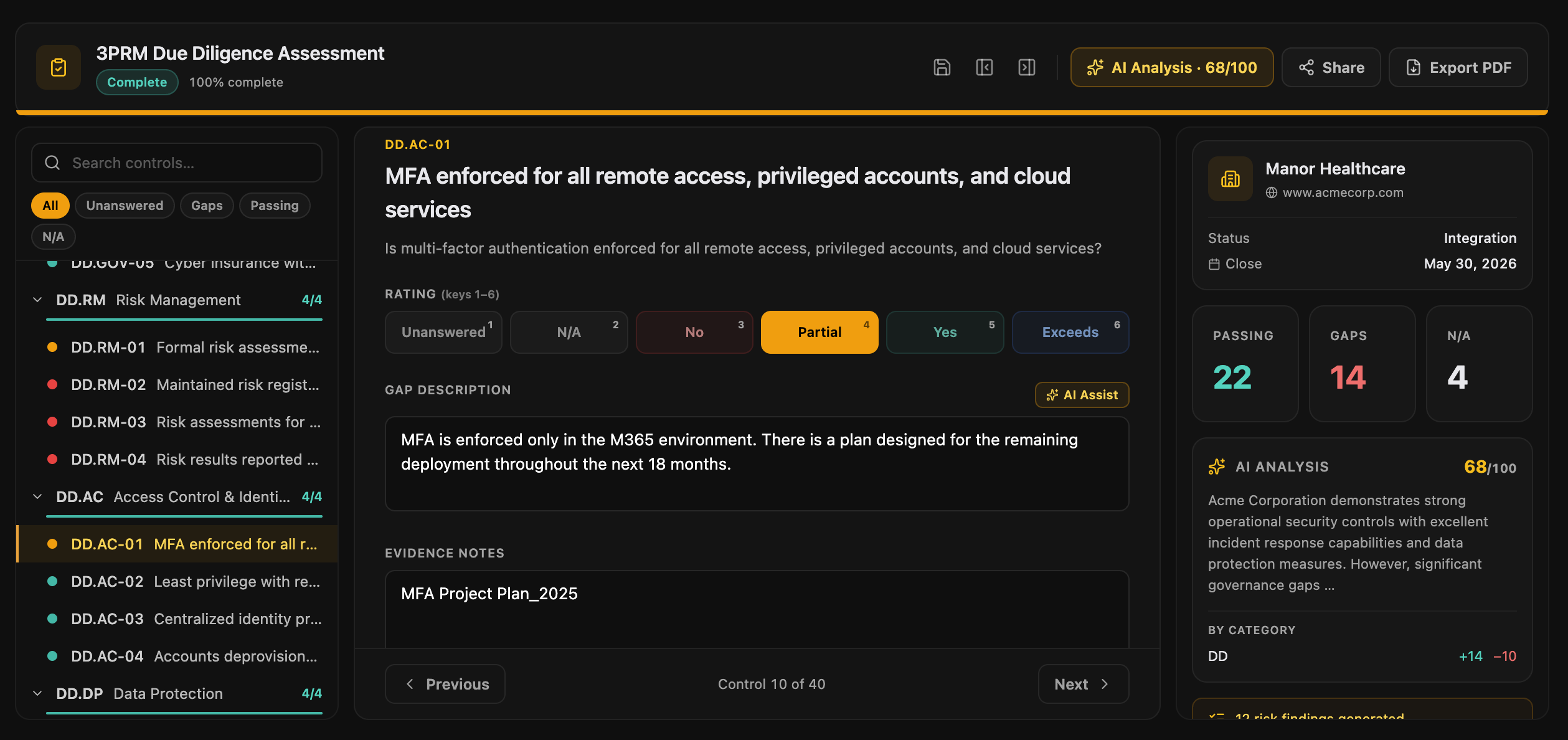
Control-by-control assessment with AI scoring
Structured assessments mapped to the frameworks that matter. Send fill-in links to target-company respondents, track status across the team, attach evidence with automatic PDF and DOCX text extraction, and let AI draft the gap descriptions and composite score. All in one place, all in one report.
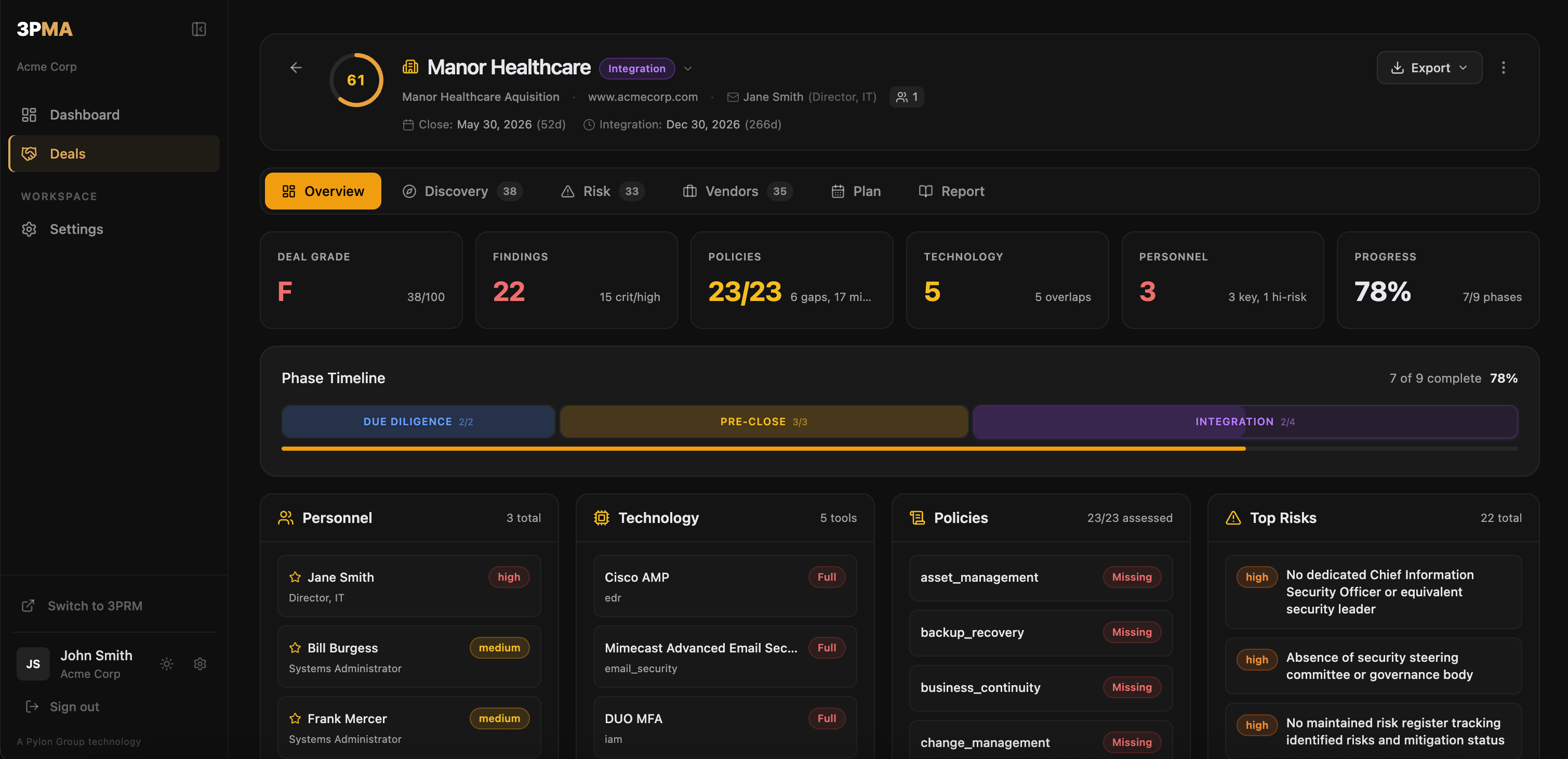
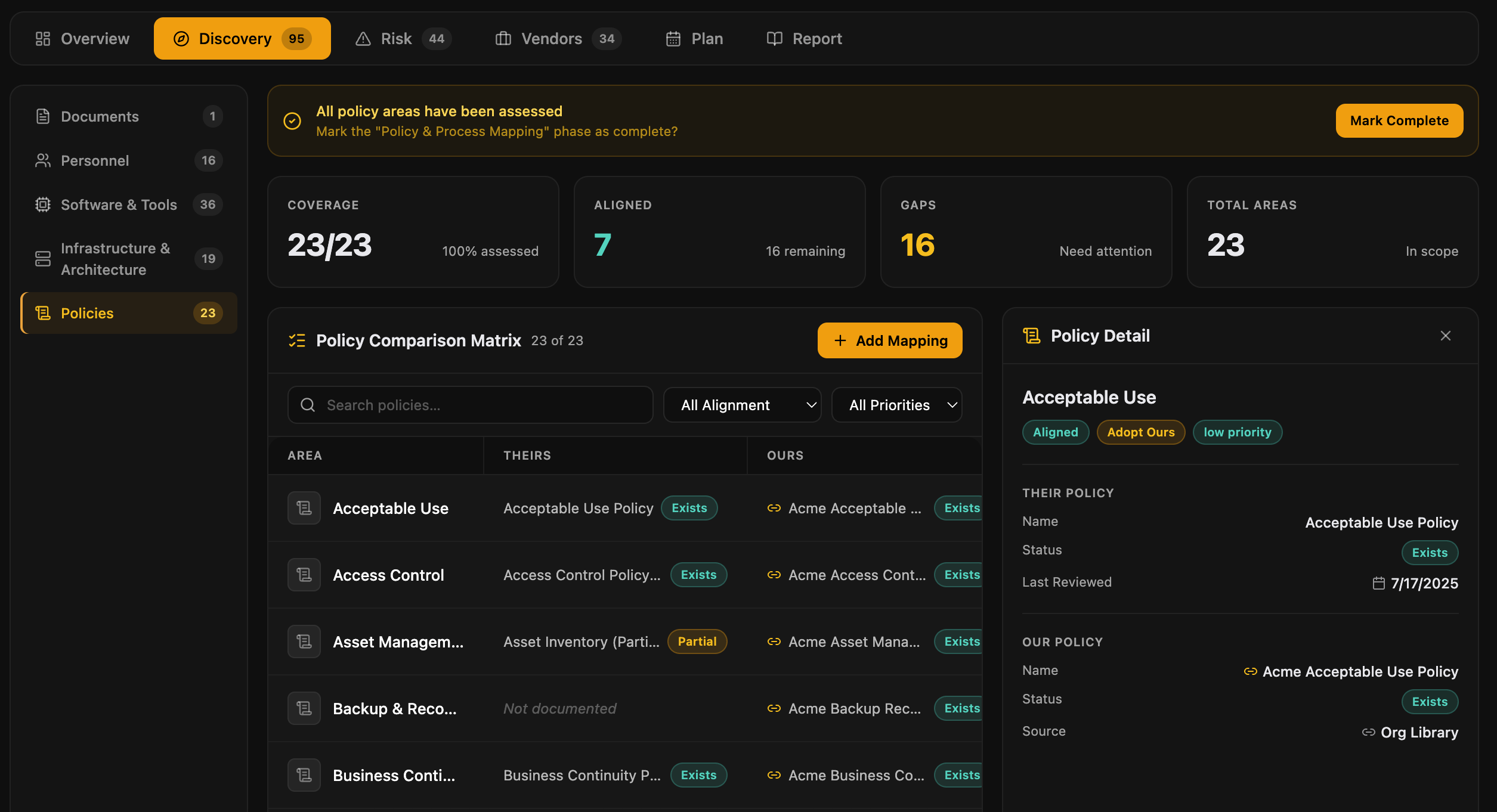
Know exactly what you're inheriting
Side-by-side comparison of the target's policies against your own. Instantly see alignment gaps, missing policies, and critical areas requiring remediation before close.
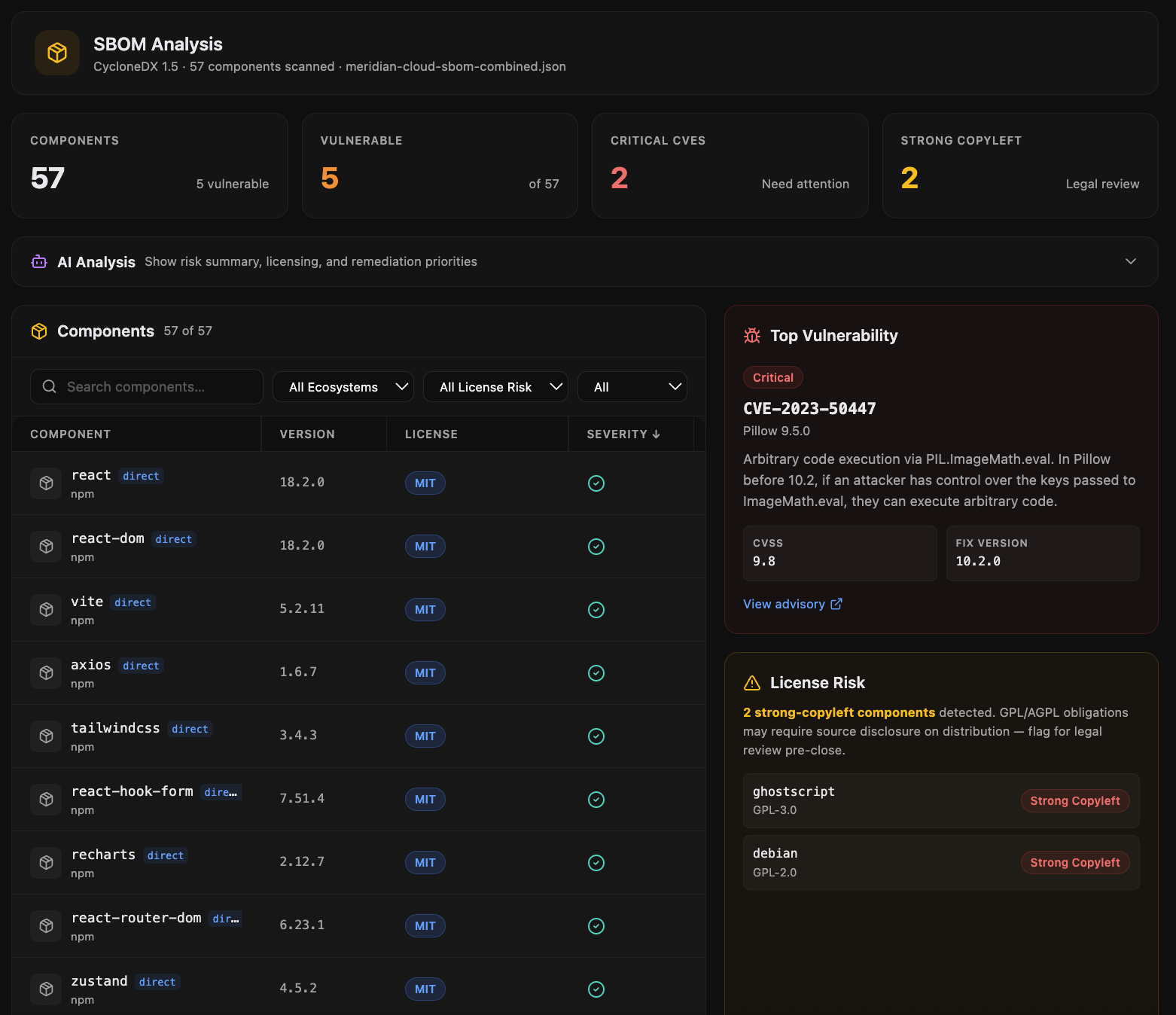
See the software risk you'd be acquiring
Upload an SBOM and get instant CVE analysis across every component. License risk classification, vulnerability severity breakdown, and AI-powered findings. The technical risk view that doesn't fit in a data room.
Assessment to investment committee in one click
Generate a DD Intelligence Report with composite scoring, weighted risk components, executive summary, and full findings detail. The artifact you hand to the IC, the GP, or the board.
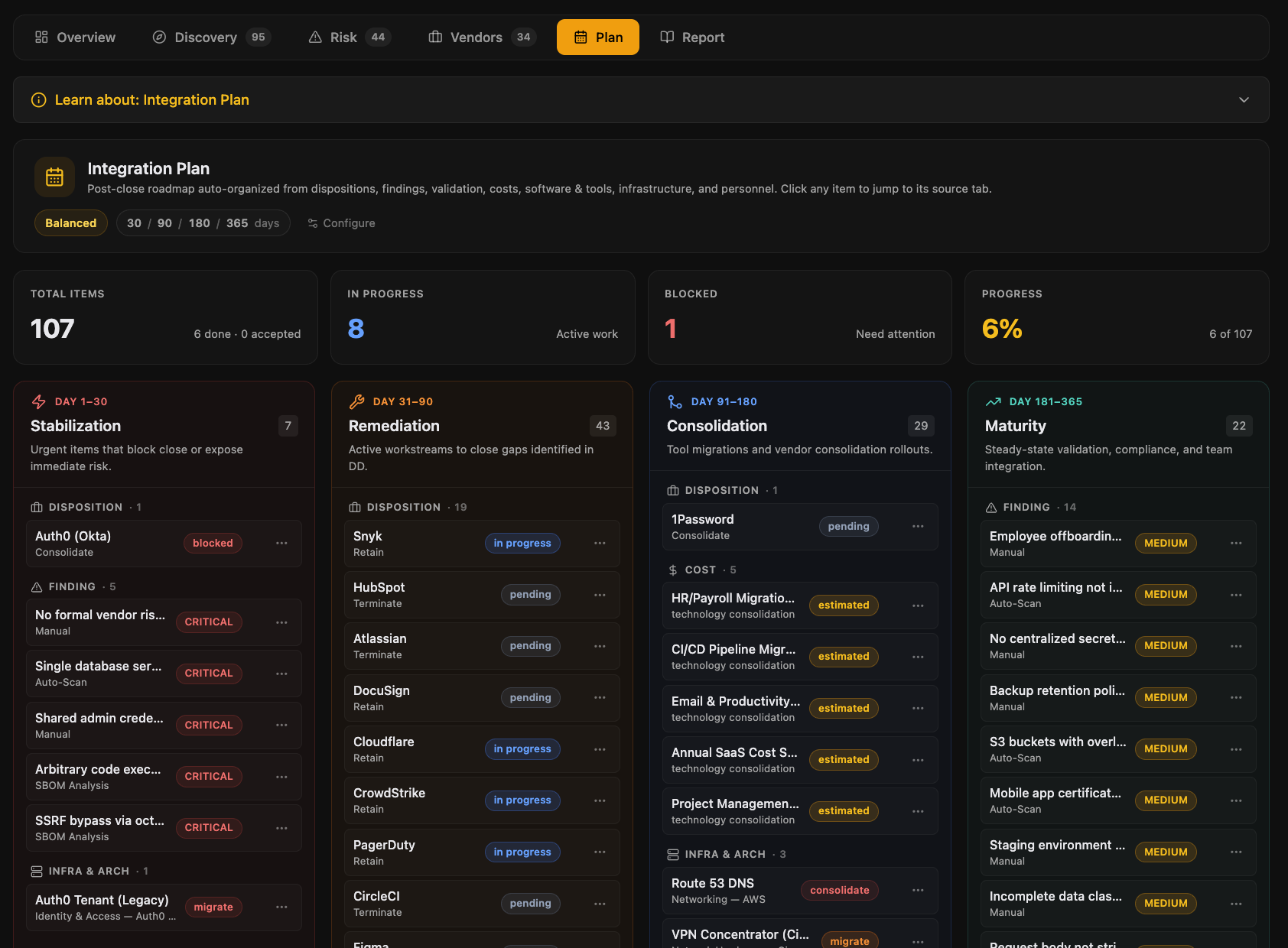
Diligence becomes the integration plan
The findings, vendor dispositions, and cost estimates that justified the deal auto-organize into a 4-phase post-close roadmap. Configurable risk tolerance, accepted risks logged with an audit trail, and the same workspace that ran DD now runs Day 1 and beyond.
One platform from first look to full integration
Diligence doesn't end at signing. 3PMA stays with the deal through Day 1 and beyond.
Built by a CISO who's run tech and security DD on both sides of the deal
3PMA was built by a practicing CISO who has led tech and security due diligence on both sides of the M&A table. Every feature exists because it was needed in a real deal, not because it sounded good in a roadmap.
Read the story →Ready to see what you're acquiring?
Schedule a 30-minute walkthrough with the founder. We'll show you 3PMA on a real deal.